Sometimes you may want to add simple user authorization to your site, but it’s unlikely or impossible to use Windows users system. In such case a suitable solution is offered by HTTP authentication/authorization system implemented in Helicon Ape mod_auth fellowship.In this article we’ll show how to enable basic authentication for the part of the site not applying much efforts.
Task specification
Protect secret directory in the root of the site via basic authentication. The directory contains index.html file that is displayed upon request http://localhost/secret/.Allow access to this directory to users bill, george and barack. Set passwords for these users.
Enabling necessary modules
For this task we’ll need mod_auth_basic,mod_authn_file and mod_authz_user modules.To enable them you simply need to uncomment corresponding lines in httpd.conf – Helicon Ape global configuration file:
LoadModule auth_basic_module modules/mod_auth_basic.so
LoadModule authn_file_module modules/mod_authn_file.so
LoadModule authz_user_module modules/mod_authz_user.soThis may be accomplished in Helicon Ape Manager.
Editing .htaccess
In Helicon Ape Manager find and click on secret directory in IIS tree. Empty .htaccess will be created and opened for this directory. We’ll add the following lines:
# Authentication type
AuthType Basic
# Name of area authentication will be used for (aka realm)
AuthName "secret area"
# Authentication provider. Here - mod_authn_file
AuthBasicProvider file
# Info for mod_authn_file - path to password file
AuthUserFile c:\inetpub\.htpasswds
# Access will be granted to all authenticated users
Require valid-userCreating passwords file
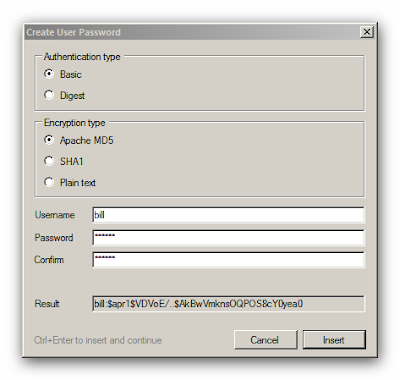
Create a new file in Helicon Ape Manager (Ctrl+N). Run the Password generator utility:Options -> Insert User Password… (or F5). Enter user name and password with confirmation.
To paste resulting string with username and password press Ctrl+Enter.Repeat this procedure for all users (remember: bill, george and barack?). Here’s what you should get:
Now save the file with the name specified in AuthUserFile directive: c:\inetpub\.htpasswds.
Testing
For testing let’s put http://localhost/secret/ into the address bar. This may be done faster by right-clicking on secret folder in IIS tree (in Helicon Ape Manager) and selecting “Browse *:80 (http)“.
The browser will prompt us to enter user credentials (username and password).
If the data you entered are correct, the server will give you the content of index.html page from secret directory.
Conclusion
Having performed such unsophisticated actions we have protected secret directory using basic authentication. We have created users by ourselves in c:\inetpub\.htpasswds file and you may add as many of them as you like. These users have nothing to do with Windows users. The name of authenticated user is accessible from server scripts (e.g., ASP or PHP) via AUTH_USER server variable.
Important note!
Authentication data (user name and password) are transfered through the network in non-encrypted form, so it’s not really safe. Secure authentication is either basic authentication via secured http (https) ordigest authentication via http.